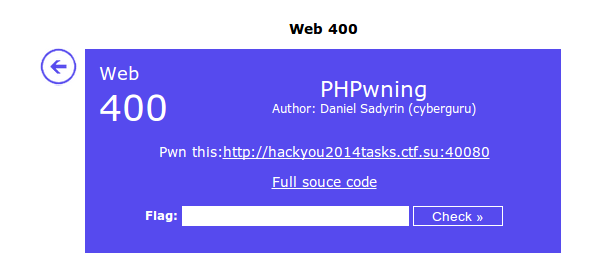
hack you 2014 CTF Writeup – Winning PHPwning Web400 the Wrong Way
This is a story about how I won hack you 2014’s Web 400 challenge the wrong way.
Using only this part of the code I was able to get the key:
<?php include 'config.php'; include 'classes.php'; $action = (isset($_REQUEST['action'])) ? $_REQUEST['action'] : 'View'; $param = (isset($_REQUEST['param'])) ? $_REQUEST['param'] : 'index'; $page = new $action($param); echo $page; ?>
I thought the correct answer had to do with using an internal PHP class and passing it a single argument.
So I searched through the PHP docs for a class with the following:
- valid/useful toString method
- requires only one input
- native on all PHP installs
After my eyes starting bleeded I had two pretty usable internal classes:
- SplFileObject – http://www.php.net/manual/en/class.splfileobject.php
- GlobIterator – http://www.php.net/manual/en/class.globiterator.php
With SplFileObject I can read the first line of any file I specify – which is pretty neat but turned out to be unneeded. As it turns out GlobIterator was good enough to win this challenge.
After doing the following I found the key just sitting in the root directory (waiting for me, daww):
![]()
Which gave me:
![]()
But why?
GlobIterator will return the first file in a directory if you just pass it a path as a single argument. This is neat because I can enumerate all files in a directory by doing:
http://127.0.0.1/web400/index.php?param=/a*&action=GlobIterator
http://127.0.0.1/web400/index.php?param=/b*&action=GlobIterator
http://127.0.0.1/web400/index.php?param=/c*&action=GlobIterator
etc…
Until I find all files in a directory.
I didn’t have to actually write that script because ASCII ‘C’ was first before other files so it just worked with “param=/*”
There’s probably a lesson here about unintended features or something but I’m too tired to think of it.
It was only afterwards that I was told this wasn’t the actually way to do it. Oops!
